Coinbase Experiences Insider Threat? $300 Million Scam Revealed, User Data Accurately Leaked
Original Title: "Over $300 Million Lost in One Year, Coinbase Users Repeatedly Targeted by Sophisticated Scams, Is There an Insider Leak Behind the Scenes?"
Original Author: Fairy, ChainCatcher
"Hello, this is the Coinbase Security Team. We have detected unusual activity on your account..."
The voice on the other end of the phone is professional and urgent, able to accurately state your name, registered email, and recent transaction history. Will you choose to hang up immediately, or follow the "customer service" guidance to gradually transfer your funds to a so-called "secure wallet"?
Recently, multiple Coinbase users have been consecutively scammed, with staggering losses. In March alone, the stolen funds have exceeded $46 million, and the annual losses for Coinbase users due to social engineering scams have reached over $300 million.
However, how exactly have these hackers been able to precisely target their victims? How have they obtained users' personal information? This security crisis may be even more severe than imagined.
Rampant Scams, Industrialized Phishing Attacks
On March 28, blockchain detective ZachXBT revealed that in the past two weeks, there have been multiple suspected cases of Coinbase users falling victim to scams, resulting in a total stolen amount in March exceeding $46 million.
In fact, such scams have long been evident. As early as the beginning of February, ZachXBT had previously disclosed that between December 2024 and January 2025, Coinbase users had lost as much as $65 million due to similar tactics, putting Coinbase at risk of facing over $300 million in social engineering scam losses annually.
According to ZachXBT's analysis, the scam tactics have formed a mature industrial chain:
1. Fraudsters Impersonate Coinbase Official
The scammers use a spoofed phone number to call the victim and leverage the user's personal information to gain trust. They claim that the user's account has experienced unauthorized login attempts, leading the victim to cooperate with security verification.
2. Sending Phishing Emails
The scammers send fake Coinbase emails containing a forged Case ID.
3. Guide User to Transfer Funds
The scammer asks the victim to transfer funds to a Coinbase Wallet and whitelist a scam address, claiming this is a form of account security verification.
4. Clone Coinbase Website
The scammer creates an almost 1:1 replica of the Coinbase phishing website and sends different operation prompts to the victim through forged emails and a Telegram scam panel.
In addition, according to Cointelegraph, several cryptocurrency users have recently received scam emails impersonating Coinbase and Gemini. These emails usually claim that due to regulatory requirements, users must transition to a self-hosted wallet and set April 1 as the deadline to create a sense of urgency.
The emails provide links to download the Coinbase Wallet or Gemini Wallet, along with pre-generated recovery phrases. Once users use these phrases to create a new wallet and transfer assets, the funds are instantly emptied by the scammer.
Internal Data Access Issues Surface
The core of social engineering scams lies in precise information gathering. In the Coinbase user scam cases, the attackers seem to have had access to victims' personal information, including phone numbers, email addresses, transaction records, etc. This raises a key question: how did this data fall into the hands of scammers?
Yesterday, The Block co-founder Mike Dudas claimed to have received an email from Coinbase on the X platform. The content of this email was unsettling, pointing directly to internal data access issues. The email stated:
"We are writing to inform you that we have detected signs indicating that a Coinbase employee may have accessed a small number of Coinbase customer accounts' records in a manner not consistent with internal policies, including your account."
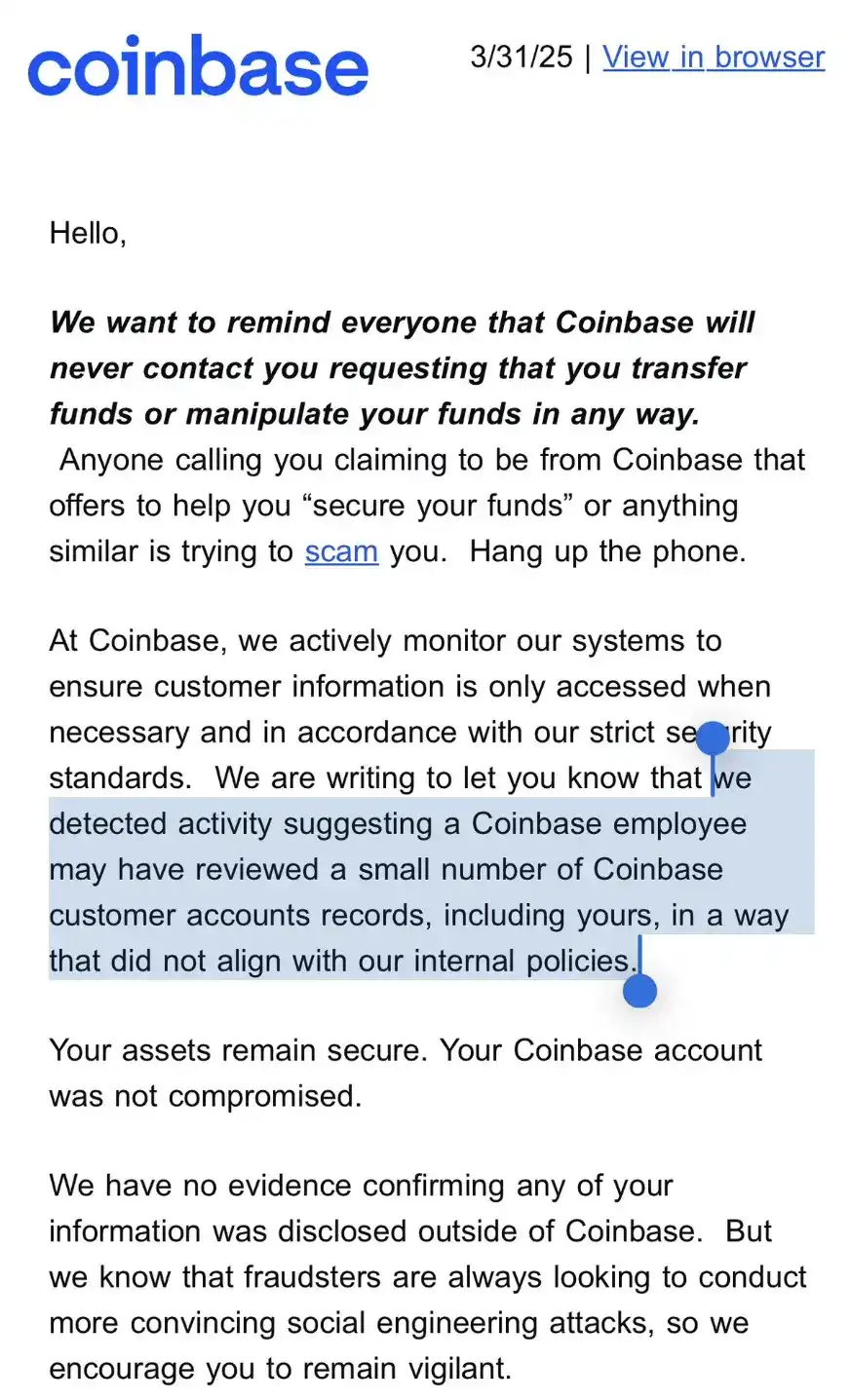
While the email stated, "Your assets remain secure, and your Coinbase account has not been compromised," and emphasized that there is currently no evidence of data leakage to external parties, this email issued a clear warning to users: internal data access issues have been confirmed and are not isolated incidents.
Dudas stated that this explains the phishing emails and calls pretending to be from Coinbase.
However, the scope of the data breach is questionable and may involve a larger set of users. Community user @ghaiankur stated: "I don't have any funds on Coinbase, and I have never used it. Yet I still received these emails because I have an account, so this may not just be targeting a few specific accounts but the entire database."
Data Breaches as an Industry Risk
Not only Coinbase, other exchanges also seem to face similar internal security vulnerabilities.
After Dudas shared the email, crypto trader Jordan Fish (@Cobie) revealed that the crypto exchange Kraken recently experienced a similar attack. He speculated: "This could be the attackers' strategy — to infiltrate the customer support team and internally steal user data."
Meanwhile, on March 27, the dark web news site Dark Web Informer disclosed that a hacker codenamed AKM69 claimed to have obtained a significant amount of private information of Gemini exchange users. The database contains 100,000 records, including the full names, emails, phone numbers, and locations of U.S. users, and even some data from Singapore and the U.K.

Either learn to protect users, or be abandoned by users.
When commenting on this incident, Solana co-founder toly suggested that exchanges should implement user-controlled transfer time locks to reduce the risk of assets being rapidly stolen. However, the essence of this event goes beyond that, exposing the internal risk control failures of exchanges and the highly industrialized nature of fraud.
Exchange security is no longer just a technical protection issue but also a matter of management and trust. In the face of increasingly sophisticated attack methods, establishing a more comprehensive risk control system will determine the future security standards of the industry.
You may also like

Social Capital CEO: How Equity Tokenization is Reshaping Capital Markets from US Stocks to SpaceX?

CoinGecko Report: Surge of 346% vs Dip of 20.8%, The Wild Rise of DEX

a16z: The Real Opportunity of Stablecoins Lies Not in Disruption but in Filling Gaps

Mining Exodus: Someone Holds $12.8 Billion AI Order

March 6 Market Key Intelligence, How Much Did You Miss?

a16z: The True Opportunity of Stablecoins is in Complementing, Not Disrupting

Predict LALIGA Matches, Shoot Daily & Win BTC, USDT and WXT on WEEX
The WEEX × LALIGA campaign brought together football excitement and crypto participation through a dynamic interactive experience. During the event, users predicted matches, completed trading tasks, and took daily shots to compete for rewards including BTC, USDT, WXT, and exclusive prizes.

Ray Dalio Dialogue: Why I'm Betting on Gold and Not Bitcoin

Who Took the Money in the AI Era? A Must-See Investment Checklist for HALO Asset Trading

Wall Street Bears Target Ethereum: Vitalik In the Know Takes Flight, Tom Lee Remains Bullish

Pump.fun Hacker Steals $2 Million, Receives 6-Year Prison Sentence, Opts for 'Self-Detonation'

6% Annual Percentage Yield as Musk Declares War on Traditional Banks

36 years, 4 wars, 1 script: How does capital price the world in conflict?

Mining Companies' Great Migration: Some Have Already Secured $12.8 Billion in AI Orders
What Is Vibe Coding? How AI Is Changing Web3 & Crypto Development
What is vibe coding? Learn how AI coding tools are lowering the barrier to Web3 development and enabling anyone to build crypto applications.

The parent company of the New York Stock Exchange strategically invests in OKX: The intentions behind the $25 billion valuation

WEEX P2P update: Country/region restrictions for ad posting
To improve ad security and matching accuracy, WEEX P2P now allows advertisers to restrict who can trade with their ads based on country or region. Advertisers can select preferred counterparty locations for a safer, smoother trading experience.
I. Overview
When publishing P2P ads, advertisers can now set the following:
Allow only counterparties from selected countries or regions to trade with your ads.
With this feature, you can:
Target specific user groups more precisely.Reduce cross-region trading risks.Improve order matching quality.
II. Applicable scenarios
The following are some common scenarios:
Restrict payment methods: Limit orders to users in your country using supported local banks or wallets.Risk control: Avoid trading with users from high-risk regions.Operational strategy: Tailor ads to specific markets.
III. How to get started
On the ad posting page, find "Trading requirements":
Select "Trade with users from selected countries or regions only".Then select the countries or regions to add to the allowlist.Use the search box to quickly find a country or region.Once your settings are complete, submit the ad to apply the restrictions.
When an advertiser enables the "Country/Region Restriction" feature, users who do not meet the criteria will be blocked when placing an order and will see the following prompt:
If you encounter this issue when placing an order as a regular user, try the following solutions.
Choose another ad: Select ads that do not restrict your country/region, or ads that allow users from your location.Show local ads only: Prioritize ads available in the same country as your identity verification.
IV. Benefits
Compared with ads without country/region restrictions, this feature provides the following improvements.
Aspect
Improvement
Trading security
Reduces abnormal orders and fraud risk
Conversion efficiency
Matches ads with more relevant users
Order completion rate
Reduces failures caused by incompatible payment methods
V. FAQ
Q1: Why are some users not able to place orders on my ad?
A1: Their country or region may not be included in your allowlist.
Q2: Can I select multiple countries or regions when setting the restriction?
A2: Yes, multiple selections are supported.
Q3: Can I edit my published ads?
A3: Yes. You can edit your ad in the "My Ads" list. Changes will take effect immediately after saving.

